IoT remote access SSH example Ubuntu has become increasingly important as more businesses and individuals adopt Internet of Things (IoT) technologies. Secure Shell (SSH) is one of the most reliable methods for remotely accessing IoT devices, ensuring secure communication between networks. Whether you're a beginner or an experienced user, understanding how to set up and manage SSH connections on Ubuntu is crucial for maintaining the security and functionality of your IoT infrastructure.
As IoT devices continue to proliferate, the need for secure remote access grows exponentially. Without proper security measures, these devices can become vulnerable to cyberattacks, data breaches, and unauthorized access. This comprehensive guide will walk you through the process of setting up SSH on Ubuntu, configuring it for IoT remote access, and ensuring your network remains secure.
This article is designed to help you understand the fundamentals of SSH and its application in IoT environments. By following the steps outlined here, you'll be able to establish a secure connection to your IoT devices using Ubuntu, ensuring that your data remains protected while maximizing operational efficiency.
Read also:Allmovieshub Hd Your Ultimate Destination For Highquality Movies
Table of Contents
- Introduction to SSH
- Why SSH for IoT?
- Setting Up SSH on Ubuntu
- Configuring SSH for Security
- Connecting to IoT Devices
- SSH Best Practices
- Troubleshooting Common Issues
- Advanced SSH Configurations
- Integrating SSH with IoT Platforms
- Conclusion and Next Steps
Introduction to SSH
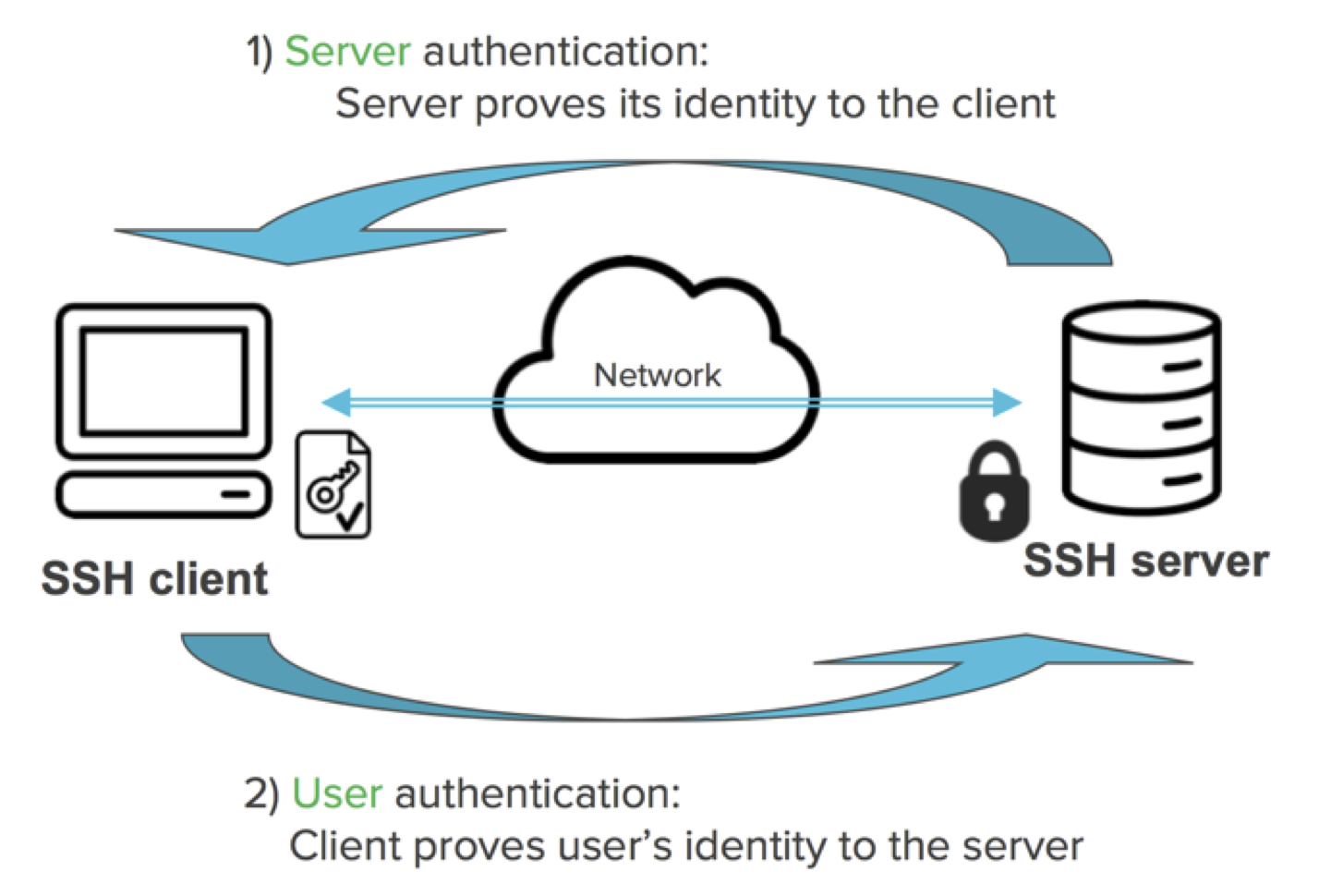
Secure Shell (SSH) is a cryptographic network protocol designed to provide secure communication over an unsecured network. It allows users to remotely access servers, devices, and systems while ensuring that data transmitted between the client and server remains encrypted and secure. SSH is widely used in IT environments, including IoT setups, due to its robust security features.
Key Features of SSH:
- Data encryption to protect sensitive information.
- Authentication mechanisms to verify user identity.
- Support for various cryptographic algorithms.
- Secure file transfer capabilities.
For IoT remote access SSH example Ubuntu, the protocol plays a critical role in enabling secure communication between IoT devices and central servers, ensuring that commands and data exchanges are protected from unauthorized access.
Why SSH for IoT?
IoT devices often operate in environments where security is paramount. Using SSH for IoT remote access provides several advantages:
Enhanced Security
SSH encrypts all data transmitted between devices, making it nearly impossible for attackers to intercept or tamper with the information. This is especially important for IoT devices that handle sensitive data.
Reliability
SSH connections are highly reliable, ensuring that commands and data are transmitted accurately and efficiently. This reliability is crucial for IoT applications where downtime or data loss can have significant consequences.
Read also:Maurice Benard Net Worth Exploring The Wealth And Legacy Of A Tv Icon
Scalability
SSH can be easily scaled to accommodate large numbers of IoT devices, making it an ideal solution for enterprises with extensive IoT networks.
Setting Up SSH on Ubuntu
To use SSH for IoT remote access, you'll first need to set up SSH on your Ubuntu system. Follow these steps to install and configure SSH:
Step 1: Install SSH Server
Open a terminal window and run the following command to install the OpenSSH server:
sudo apt update
sudo apt install openssh-server
Step 2: Verify SSH Installation
Once the installation is complete, verify that the SSH service is running by using the following command:
sudo systemctl status ssh
Step 3: Configure Firewall
Ensure that your firewall allows SSH traffic by running the following command:
sudo ufw allow ssh
Configuring SSH for Security
While SSH is inherently secure, additional configuration can further enhance its protection:
Disable Root Login
Disallowing root login reduces the risk of unauthorized access. Edit the SSH configuration file:
sudo nano /etc/ssh/sshd_config
Set "PermitRootLogin no" and save the file.
Use Strong Passwords or Keys
Enforce strong passwords or, preferably, use SSH keys for authentication. Generate an SSH key pair using the following command:
ssh-keygen -t rsa -b 4096
Limit User Access
Restrict SSH access to specific users or groups by modifying the SSH configuration file:
AllowUsers username
Connecting to IoT Devices
Once SSH is configured on your Ubuntu system, you can connect to IoT devices using the following steps:
Step 1: Obtain Device IP Address
Identify the IP address of the IoT device you wish to connect to.
Step 2: Establish SSH Connection
Use the SSH command to connect to the device:
ssh username@device_ip
Step 3: Authenticate
Enter your password or use an SSH key to authenticate the connection.
SSH Best Practices
To ensure the highest level of security and efficiency when using SSH for IoT remote access, follow these best practices:
- Regularly update SSH software to patch vulnerabilities.
- Monitor SSH logs for suspicious activity.
- Implement two-factor authentication for added security.
- Limit SSH access to trusted networks or IP addresses.
Troubleshooting Common Issues
Even with proper configuration, issues may arise when using SSH for IoT remote access. Here are some common problems and their solutions:
Connection Refused
Ensure that the SSH service is running and that the firewall allows SSH traffic.
Authentication Failure
Verify that the username and password are correct or that the SSH key is properly configured.
Timeout Errors
Check the network connection and ensure that there are no routing issues between the client and server.
Advanced SSH Configurations
For advanced users, SSH offers several configuration options to enhance its functionality:
Port Forwarding
Set up port forwarding to access services running on IoT devices securely.
SSH Tunnels
Create encrypted tunnels for secure communication between devices.
SSH Proxy Commands
Use proxy commands to route SSH traffic through intermediate servers for added security.
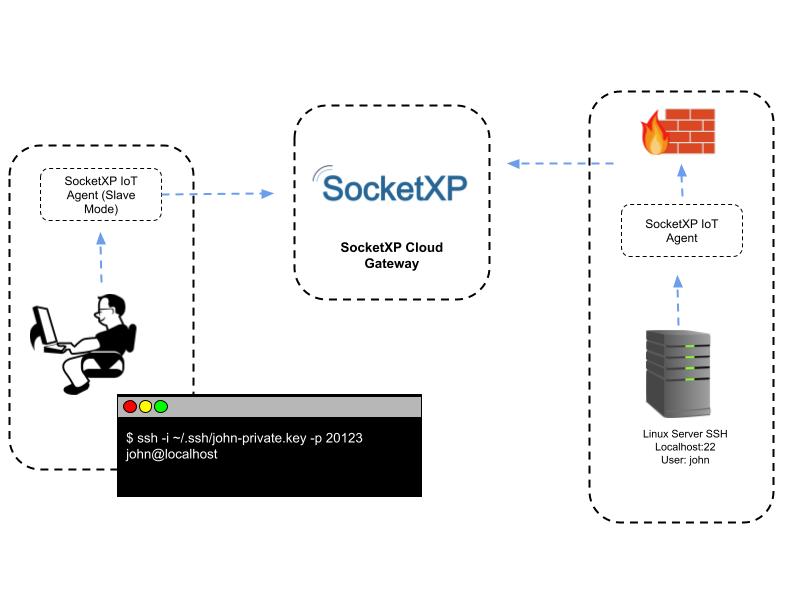
Integrating SSH with IoT Platforms
Many IoT platforms support SSH integration, allowing users to manage devices remotely with ease. Some popular platforms include:
- Amazon Web Services (AWS) IoT
- Microsoft Azure IoT
- Google Cloud IoT
These platforms provide tools and APIs to simplify the integration process, ensuring seamless SSH connectivity for IoT devices.
Conclusion and Next Steps
IoT remote access SSH example Ubuntu demonstrates the importance of secure communication in IoT environments. By following the steps outlined in this guide, you can set up and configure SSH on Ubuntu to ensure that your IoT devices remain secure and functional.
To further enhance your knowledge and skills, consider exploring advanced SSH configurations and integrating SSH with IoT platforms. Additionally, stay updated on the latest security trends and best practices to protect your IoT infrastructure.
We encourage you to share your thoughts and experiences in the comments section below. If you found this guide helpful, please consider sharing it with others who may benefit from it. For more information on IoT and SSH, explore our other articles on the site.
References:
- OpenSSH Documentation - https://www.openssh.com/manual.html
- Ubuntu SSH Guide - https://ubuntu.com/server/docs
- National Institute of Standards and Technology (NIST) - https://www.nist.gov